Livebox Wpa2-psk Crack
When it comes to securing your Wi-Fi network, we always recommend WPA2-PSK encryption. There are two types of ways to potentially crack a password. How to hack wifi (WPA2-PSK) password using Kali Linux 2.0. Need an extra adapter/device or a usb for cracking a WPA2-PSK security as i have seen every person who. Jul 10, 2013 WPA2 in Windows XP SP3. Windows XP IT Pro >Windows XP Service Pack 3 (SP3). I was able to establish a connection to. Mario Kart Double Dash Iso Download Dolphin.
There is a new version of this article., we showed you how to secure your wireless with industrial strength RADIUS authentication via WPA-Enterprise. It turns out that there's a little back-story there.
So, in traditional Tarentino fashion, now that we've already seen the ending, let's back up to the beginning: cracking WPA-PSK. Wi-Fi Protected Access () was created to solve the gaping security flaws that plagued WEP.
Perhaps the most predominant flaw in WEP is that the key is not hashed, but concatenated to the IV, allowing completely passive compromise of the network. With WEP, you can literally sit in your car listening for packets on a network. Once you have captured enough of them, you can extract the key and connect to the network. WPA solves this problem by rotating the key on a per-packet basis, which renders the above method useless. However, nothing is perfectly secure, and WPA-PSK is particularly vulnerable during client association, during which the hashed network key is exchanged and validated in a 'four-way handshake'. The Wi-Fi Alliance, creators of WPA, were aware of this vulnerability and took precautions accordingly.
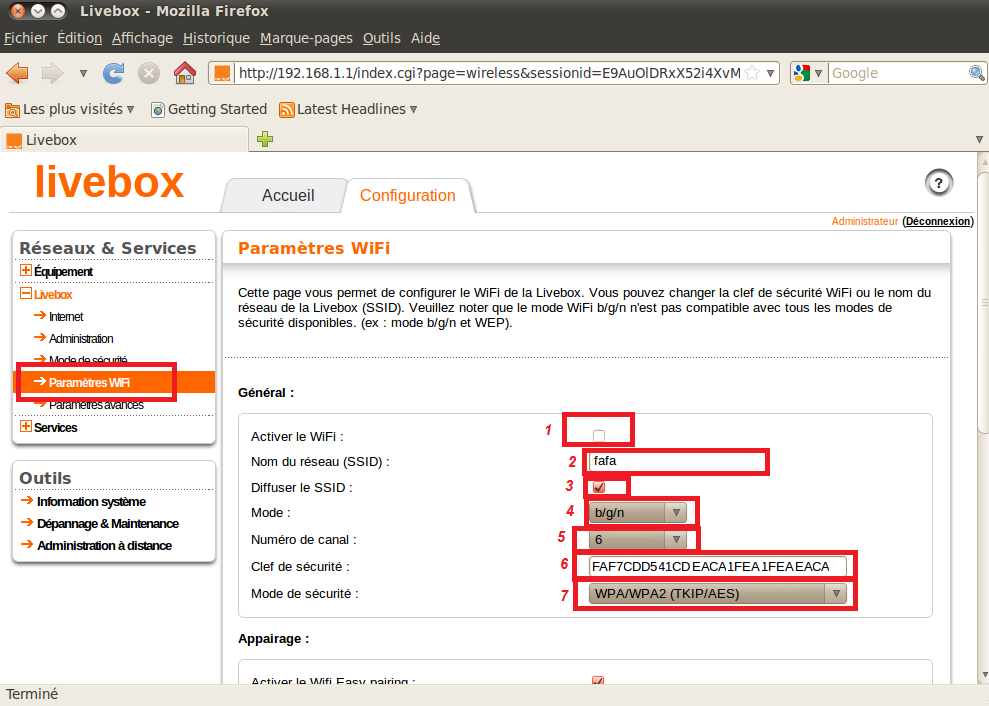
Instead of concatenating the key in the IV (the weakness of WEP), WPA hashes they key using the wireless access point's SSID as a salt. The benefits of this are two-fold. First, this prevents the statistical key grabbing techniques that broke WEP by transmitting the key as a hash (cyphertext). It also makes hash precomputation via a technique similar to more difficult because the SSID is used as a salt for the hash.
WPA-PSK even imposes a eight character minimum on PSK passphrases, making bruteforce attacks less feasible. So, like virtually all security modalities, the weakness comes down to the passphrase. WPA-PSK is particularly susceptible to dictionary attacks against weak passphrases. In this How To, we'll show you how to crack weak WPA-PSK implementations and give you some tips for setting up a secure WPA-PSK AP for your SOHO.